-png.png)
Executives building applications with open source software should familiarize themselves with the following critical government actions. Each of these is explained in more detail below.
Over the next year, US government agencies are required to comply with more stringent cybersecurity requirements that will also require organizations providing software or services to the federal government to self attest that their software also meets these requirements.
Here are some key dates that organizations should be aware of (some of which have already passed). Note that organizations will be required to self-attest that their software meets NIST standards by late 2023 (for critical software) and early 2024 (for all other software). These are the dates that agencies are accountable for. There are additional action items applicable to the Office of Management and Budget (OMB) and the Cybersecurity and Infrastructure Security Agency (CISA).
Deadline for public feedback on the proposed CISA attestation form.
As a follow-up to the National Cybersecurity Strategy from March 2023, the White House released the National Cybersecurity Strategy Implementation Plan in July 2023. This plan exists as a living document set to be updated annually and provides a roadmap for the ideas mapped out in the strategy delivered publicly in March 2023.
Organizations building applications with open source should look for impacts in the following areas:
The U.S. government Office of Management and Budget (OMB) released memorandum M-23-16 as an update to the guidance for enhancing the security of the software supply chain originally published in OMB memorandum M-22-18 in September 2022.
The dates for organizations to provide attestations around their secure development practices for critical software are adjusted as such:
M-23-16 reiterates that software producers are responsible for attesting that the secure development practices used to build their products are aligned with the NIST SSDF guidelines. It also clarifies the penalty for non-compliance: agencies must discontinue use of software that does not meet the attestation requirements or have an approved plan of action and milestones (POA&M) for achieving compliance.
.png)
On March 11, 2024, CISA released the final self-attestation form organizations selling software to the government will need to use to attest to the secure development practices they follow, as specified in OMB memorandum M-22-18.
The National Cybersecurity Strategy is the next step in a series of recent actions to improve cybersecurity for federal government agencies, the nation’s businesses, and citizens as a whole. This strategy will have an extensive impact on future policies and laws emerging from the government regarding cybersecurity.
Organizations building applications with open source should look for impacts in the following areas:
The Office of Management and Budget (OMB) guidance in M-22-18 is a direct follow-up to White House Executive Order 14028. It formalizes the NIST guidance provided in the NIST Secure Software Development Framework and NIST Software Supply Chain Security Guidance documents as the government requirements for developing secure software, and mandates federal government agencies comply with these guidelines. It also sets aggressive deadlines for compliance, both for the agencies themselves and for organizations that provide software to these agencies.
Any organization that sells software to the government will be required to self-attest that their software complies with the NIST guidelines starting in 2024. In addition:
What is an attestation?
Attestation is the “issue of a statement, based on a decision, that fulfillment of specified requirements has been demonstrated.”
In this case, organizations selling software to the government will be required to self-attest that they conform with specific secure software development standards drawn from the NIST guidelines.
Source: Software Supply Chain Security Guidance Under Executive Order (EO) 14028 Section 4e
As directed by Executive Order 14028, the National Institute of Standards and Technology (NIST) published specific guidance on secure software development standards (including for third-party software) in its NIST Secure Software Development Framework and NIST Software Supply Chain Security Guidance documents.
According to OMB memorandum M-22-18, organizations will need to self-attest that they comply with these guidelines by as soon as June 2024. Key guidelines that impact organizations developing software with open source include:

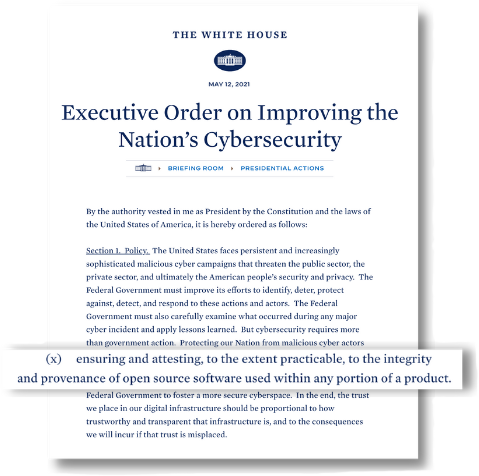
The White House issued Executive Order 14028 on Improving the Nation’s Cybersecurity in May 2021 in response to increasing digital threats like the one that impacted SolarWinds and its customers.
This order set in motion many of the other US government efforts to improve cybersecurity that are highlighted in detail on this page. It had many elements that specifically impacted organizations developing applications with open source, and set timelines for more detailed guidelines that are now beginning to emerge from NIST and the OMB.
Executive Order 14028 has numerous provisions that organizations using open source to develop applications should understand. At a high level, it states that organizations will need to begin to attest to the health, security, and provenance of the open source components that go into their applications. Among other stipulations, it recommends that organizations:
Organizations selling software or solutions to the government that include open source software components need to pay particular attention to federal self-attestation requirements outlined above as they continue to emerge. The critical question these organizations should be asking themselves is “how do I demonstrate the required ‘good-faith effort’ to maintain trusted source code supply chains for the third-party open source software components we use but do not produce ourselves?”
To comply with the requirements, organizations must better understand the security practices of the open source software they are building into their applications. Yet, the so-called open source software supply chain is not a traditional supply chain in that open source maintainers typically do not have a business relationship with their users and license their software “as-is” with no warranty.
Organizations will need to have visibility into their open source software supply chain to understand more about the components they are using and the security practices these projects follow.
Organizations will be required to make a good-faith effort to maintain trusted source code supply chains to address the security of not only the software they write, but also included third-party open source software components—which typically comprise over 70% of the code in a modern application. The hard reality is that doing the work to ensure apprpriate secure development practices are in place and correctly documented on open source projects takes time, and can get challenging to scale, especially considering most organizations typically rely on thousands of open source packages.
Tidelift has been working to address these very challenges. To show how we help organizations meet the U.S. government requirements for the open source components being used in their applications, we’ve created a sample open source attestation report using the most comprehensive database of maintainer-validated security and maintenance attestations. Tidelift is uniquely positioned to deliver this report through its partnerships with open source maintainers, who are paid to ensure their projects follow important security and maintenance practices like those found in the NIST SSDF and keep those attestations up-to-date.
Learn more about this open source attestation report or contact us to request a custom open source attestation report for the components being used in your organization.
Watch a demo on how Tidelift helps organizations meet government compliance requirements
(January 2022). In response to the fallout from the Log4Shell vulnerability, the United States Federal Trade Commission issued an alert warning...
On September 15, 2022 the EU unveiled a draft of the Cyber Resiliency Act (CRA), an eighty-seven page document detailing proposed new rules meant to...
In this recorded webinar, you will learn: