Here’s a quick list: It all started with White House cybersecurity executive order 14028; then came…
Does all that feel like alphabet soup to you? We have good news: we’re here to help.
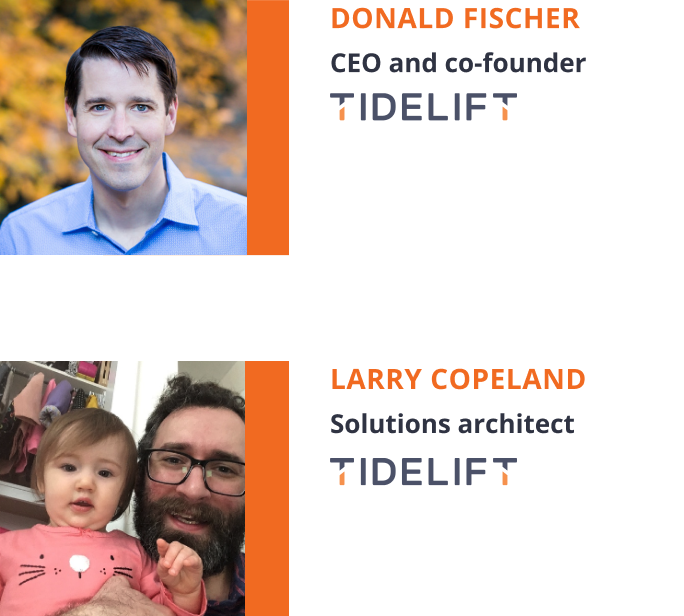
Tidelift CEO and co-founder, Donald Fischer, talked through all these government cybersecurity initiatives—specifically how they impact the third party open source software you pull into your applications, because, spoiler alert: that code will need to comply with government regulations, too. And soon, because compliance deadlines are approaching quickly.
After Donald gave you the down low on what you need to know, Tidelift solutions architect Larry Copeland gives a demo on how Tidelift can help your team comply with these government regulations so your organization can avoid putting government contracts at risk.
Copyright © Tidelift, Inc.